The Future of Secure Computing with AWS EC2 Nitro Enclaves
Introduction
In an era where data breaches and cyber threats are becoming increasingly sophisticated, the need for robust data security measures has never been more critical. While encryption has long been a staple for protecting data at rest and in transit, the challenge of securing data while it is being processed has remained a significant concern. This is where confidential computing steps in, offering a transformative approach to data security by encrypting data even while it is in use.
As part of my journey into understanding and implementing advanced data security, I recently explored AWS EC2 Nitro Enclaves. This innovative technology is paving the way for enterprises to achieve unparalleled levels of security for their sensitive workloads. Let me take you through what I learned and why it matters.
What is Confidential Computing?
Confidential computing is an emerging paradigm in data security that ensures sensitive data remains encrypted, even while it is being processed in memory. Traditional encryption methods protect data during storage and transmission, but they fall short when data is actively used by applications. Confidential computing addresses this gap by utilizing hardware-based trusted execution environments (TEEs) to create isolated, secure areas within a device’s processor.
This approach is particularly crucial for industries handling sensitive data, such as healthcare, finance, and government, where compliance and privacy regulations demand the highest levels of data protection.
Introducing AWS EC2 Nitro Enclaves
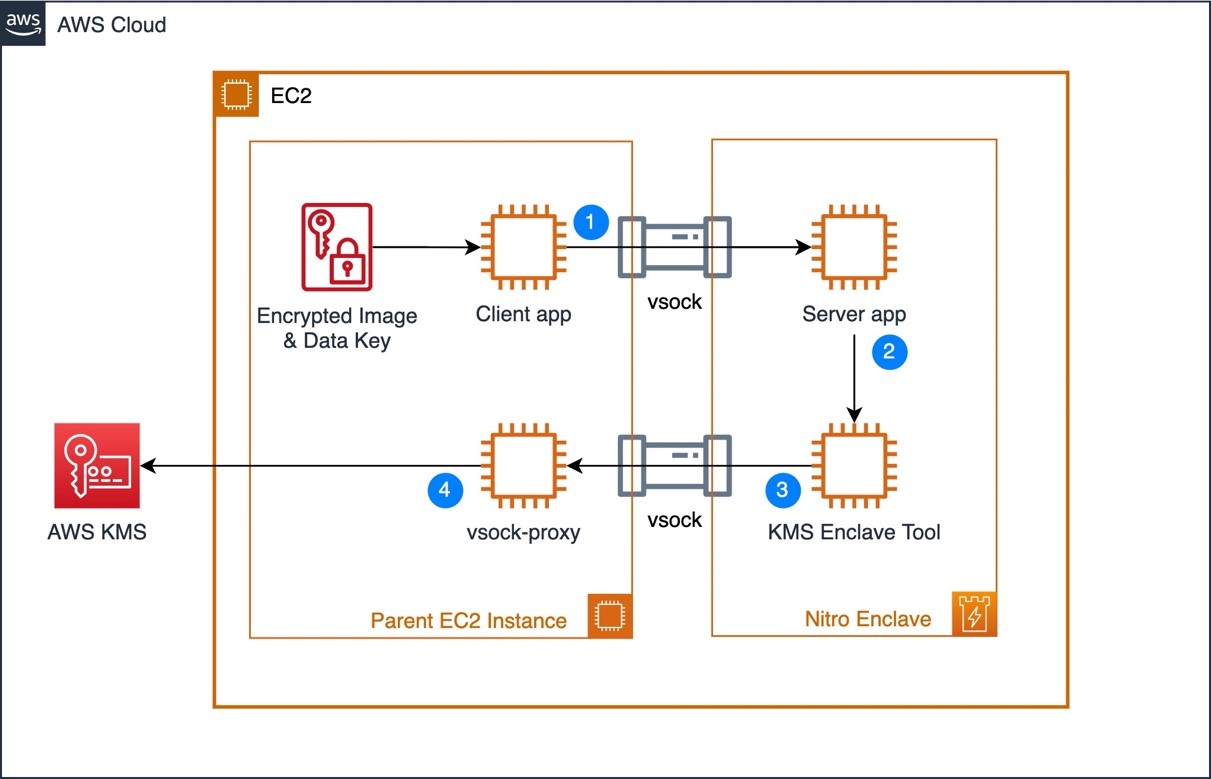
AWS EC2 Nitro Enclaves are a game-changer in the realm of confidential computing. Built on the AWS Nitro System, Nitro Enclaves provide a secure, isolated environment within an EC2 instance for processing sensitive data. Key features include:
- Memory Isolation: Nitro Enclaves use dedicated vCPUs and memory, isolating sensitive workloads from the parent instance and other processes.
- Cryptographic Attestation: Enclaves generate cryptographic attestations to verify the integrity of the software running inside them.
- KMS Integration: Nitro Enclaves work seamlessly with AWS Key Management Service (KMS) to securely manage encryption keys.
How to Implement a Simple Nitro Enclave
Below is a guide to setting up and running a simple Nitro Enclave for secure communication using Python and VSOCK:
Prerequisites
- An EC2 instance with Nitro Enclaves support enabled.
- AWS CLI configured.
- Docker installed.
- Nitro CLI installed.
Initial Setup
-
Install the required packages:
sudo amazon-linux-extras enable aws-nitro-enclaves-cli sudo yum install -y aws-nitro-enclaves-cli aws-nitro-enclaves-cli-devel sudo yum install -y docker -
Start and enable the necessary services:
sudo systemctl start docker sudo systemctl enable docker sudo systemctl start nitro-enclaves-allocator.service sudo systemctl enable nitro-enclaves-allocator.service -
Add the user to required groups:
sudo usermod -a -G docker ec2-user sudo usermod -a -G ne ec2-user
Project Structure
Create the following directory structure:
project/
├── enclave/
│ ├── Dockerfile
│ ├── enclave.py
│ └── requirements.txt
└── parent/
└── client.py
Enclave Code
-
Create
enclave/enclave.py:import socket import json import signal import sys def signal_handler(signum, frame): print(f"Received signal {signum}") sys.exit(0) def main(): signal.signal(signal.SIGTERM, signal_handler) signal.signal(signal.SIGINT, signal_handler) print("Starting server...", flush=True) client_socket = socket.socket(socket.AF_VSOCK, socket.SOCK_STREAM) client_socket.bind((socket.VMADDR_CID_ANY, 5000)) client_socket.listen(1) while True: conn, _ = client_socket.accept() payload = conn.recv(4096) if payload: response = json.dumps({"message": "Data received", "data": payload.decode()}) conn.send(response.encode()) conn.close() if __name__ == "__main__": main() -
Create
enclave/Dockerfile:FROM amazonlinux:2 RUN yum update -y && yum install -y python3 python3-pip COPY . /app/ WORKDIR /app/ CMD ["python3", "/app/enclave.py"] -
Add
enclave/requirements.txt(if needed).
Parent/Client Code
Create parent/client.py:
import socket
import json
def main():
sock = socket.socket(socket.AF_VSOCK, socket.SOCK_STREAM)
sock.connect((3, 5000)) # Replace `3` with your enclave CID
message = json.dumps({"test": "Hello from parent!"}).encode()
sock.send(message)
response = sock.recv(4096)
print("Response from enclave:", response.decode())
sock.close()
if __name__ == "__main__":
main()
Building and Running the Enclave
-
Build the Docker image:
cd enclave sudo docker build -t enclave:latest . -
Build the enclave:
nitro-cli build-enclave --docker-uri enclave:latest --output-file enclave.eif -
Run the enclave:
nitro-cli run-enclave --cpu-count 2 --memory 2340 --eif-path enclave.eif --debug-mode -
Get the enclave CID:
nitro-cli describe-enclaves -
Run the client:
python3 parent/client.py
How Nitro Enclaves Enhance Data Security
Nitro Enclaves address critical security concerns by ensuring that sensitive data remains protected across all stages:
-
Memory Encryption: Data processed within the enclave remains encrypted, safeguarding it from unauthorized access.
-
KMS Proxy Integration and Cryptographic Attestation:
Platform Configuration Registers (PCRs): PCRs play a crucial role in cryptographic attestation. They are special registers that store hash values representing the state of the enclave’s software and hardware configuration. These values are calculated during the enclave’s initialization and provide a tamper-proof representation of the enclave’s integrity.
PCR Levels:
- Static PCRs: Reflect the state of the hardware and firmware.
- Dynamic PCRs: Represent the runtime state of the software stack.
By including PCR values in a KMS key policy, organizations can restrict decryption operations to specific, verified enclave states. This ensures that sensitive data is only accessible when the enclave is in a trusted configuration.
Adding PCRs to KMS Key Policy:
- Create a condition in the key policy that specifies the required PCR values.
- Use the
kms:RecipientAttestationcondition key in the policy to enforce this requirement.
Example Policy Snippet:
{ "Version": "2012-10-17", "Statement": [ { "Sid": "AllowAccessWithAttestation", "Effect": "Allow", "Principal": { "AWS": "arn:aws:iam::123456789012:role/YourRole" }, "Action": "kms:Decrypt", "Resource": "arn:aws:kms:us-east-1:123456789012:key/your-key-id", "Condition": { "StringEquals": { "kms:RecipientAttestation:PCR0": "your-pcr-value", "kms:RecipientAttestation:PCR1": "your-pcr-value" } } } ] }Benefits: This approach reduces risks from OS-level attacks, malware, or configuration tampering, ensuring data is decrypted only in trusted environments.
-
Protection from Malware and Insider Threats: By isolating sensitive workloads, Nitro Enclaves mitigate threats from malware, rogue administrators, and other potential vulnerabilities.
For more details, you can refer to the AWS Nitro Enclaves Documentation.
Confidential Computing Across the Industry
AWS is not alone in championing confidential computing. Other major cloud providers are also making strides in this area:
- Microsoft Azure: Azure’s Confidential VMs provide secure execution environments, leveraging AMD SEV-SNP technology for memory encryption.
- Google Cloud: Google’s Confidential GKE Nodes allow users to run Kubernetes workloads in a secure, isolated environment.
These advancements underscore the growing recognition of confidential computing as a critical component of enterprise security.
Why Enterprises and SaaS Providers Should Adopt Confidential Computing
Data security is no longer optional—it is a business imperative. For enterprises handling sensitive or compliance-bound data, adopting confidential computing solutions like AWS EC2 Nitro Enclaves is essential. Similarly, SaaS providers must integrate such measures to protect customer data and build trust.
By prioritizing confidential computing, organizations can:
- Ensure compliance with stringent data protection regulations.
- Protect against a wide range of cyber threats.
- Foster customer confidence through robust security practices.
Conclusion
Confidential computing represents the future of data security, enabling organizations to process sensitive data with unparalleled protection. AWS EC2 Nitro Enclaves, along with similar offerings from other cloud providers, provide a powerful toolkit for safeguarding data in today’s threat landscape.
Every enterprise that values data security should explore confidential computing. After all, security should never be an afterthought—especially when dealing with the crown jewels of any organization: its data.
For more insights and technical details, visit the AWS Nitro Enclaves Documentation.

Leave a comment